 Display-TAN
Display-TAN

More Details
Security
A valid TAN can only generated if the money transfer data are transmitted to the bank card where they are securely visualized to the bank customer, confirmed, and finally signed via the secret key stored on the bank card.
Bluetooth attacks (no danger). All data sent to the card are AES encrypted by the bank server. The AES key is only known to the bank server and to this card (different cards have differents keys). This way, Bluetooth manipulation attacks are impossible. Likewise, sniffing of money transfer data by neighbors, colleagues, etc. is impossible.
Man-in-the Middle. More dangerous than these ''Bluetooth'' attacks is a smartphone trojan which sends during an Mobile Banking session a money transfer to the bank and also to the card which is different from the one which was entered by the bank customer, while showing the bank customer on the smartphone display the money transfer data he expects (Man-in-the-Middle attack). This attack will - hopefully - be discovered by the bank customer during the visualization on the card which will show the malicious money transfer data. This attack is dangerous and it demonstrates that the customer has to check the data shown on the card's display carefully, otherwise the security provided by the display card is in vain.
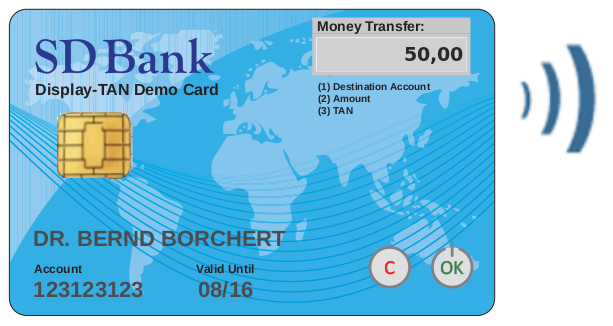
Social Engineering. The remaining attacks on the Display-TAN method are the so-called ''social engineering'' attacks. These attacks are trying to get a TAN from the customer and his bank card by misleading him, for example, by telling him that a certain money transfer is just a testing procedure of the bank, or it is a lottery, or something like this. In order to prevent Social Engineering attacks, the bank may show to the customer on the card's display a text which makes clear that he/she is in fact dealing with a real money transfer, and let this confirm via OK. Because letters are not readable very well on the display - even not on a 14-segment display - the current solution is to print the information that the customer is dealing with a real money transfer onto the card, preferably in a way such that it looks like a part of the display, see the text ''Money Transfer:'' on the current demo card on top of this page.
Security summary. Summarizing, the only potentially succesful attacks on Display-TAN are a Man-in-the Middle attack expecting the unattentiveness of the bank customer, and Social Engineering attacks. These are the same ones as the potential attacks on Chip-TAN, in other words, Display-TAN has the same high level of security as Chip-TAN.
A security/usability comparison of Mobile Banking methods: pdf
Legal aspects/damage compensation. Like with Chip-TAN, the only successful attacks on Display-TAN are Social Engineering and a Man-in-the Middle expecting the unattentiveness of the bank customer. Note that the customer behaviour can in these cases be interpreted as ''grossly negligent'', and the bank knows that the customer has made a mistake and can show this. Therefore, the bank does not have to compensate the financial damage of the customer. This does not hold for other Online Banking methods: A fraud with SMS-TAN, iTAN, App-based methods, and also NFC-TAN can usually not be proven by the bank to be caused by a mistake by the bank customer, in fact a fraud could always possibly be the result of a trojan attack while the bank customer has done everything perfectly right. Summarizing: ChipTAN and Display-TAN do not in a 100% way prevent from fraud - but they prevent the bank from paying for it! - while with the other methods the bank has to compensate nearly every case of fraud damage.
Usability
No extra device. The main usability advantage of Display-TAN is that only the bank card and a smartphone is necessary for it - no extra device is needed.
True Mobility. Mobile Banking with Display-TAN in fact corresponds to the idea of ''mobility'', i.e. independence of anything not usually carried in the user's pockets.
Comparison with ChipTAN. An advantage of Display-TAN as compared to the ChipTAN method is that reading the money transfer data via 2D-code and Bluetooth is much more easy than reading it via the flickering code, especially in the Mobile Banking case.
Comparison with SMS-TAN. Compared to SMS-TAN, Display-TAN may be a bit less convenient for the bank customer during Online Banking, but Display-TAN has for Online Banking the usability advantage that it also works in case the smartphone is offline. SMS-TAN Mobile Banking is for security reasons not available, at least not in Germany. In other words: The measure against the security disadvantage of SMS-TAN becomes a convenience disadvantage of SMS-TAN.
Smartphone-TAN (= App-TAN)
For a comparison of Display-TAN with Smartphone-TAN (= App-TAN) in terms of security/usability/costs, see this extra page.
Integration of Display-TAN into the bank card
Part of the Banking Card. The recommended standard procedure is the following: A plastic card containing everything what is needed for the Display-TAN part of a bank card, including display, buttons, battery, antenna, processor, etc., is produced in Taiwan. These display cards are send - not yet personalized - to the card printing location of the bank. There, the core bank chip is mounted onto the display card - here the display cards are taken instead of the standard plastic cards, i.e., a change of the chip mounting process is not necessary. The display card chip and the core bank chip do not have any electrical connection. Finally, the core bank chip and the display card chip are personalized, via contact resp. via BLE.
In case the core bank chip is NFC-capable, an additonal NFC antenna and an access point for it is supplied within the inlay card. The NFC antenna is not connected to the inlay. The NFC antenna and the BLE antenna can coexist.
Extra card. A variant is that the Display-TAN card is delivered to the bank customer as an extra card, in addition to the bank card. This is less convenient for the bank customer because he has to carry two cards. This variant is also less secure because a loss of the extra card may be not noticed or be ignored by the bank customer. Moreover, the costs for this variant are higher because of package/postage and the process costs emerging in case of card loss. Summarizing, this variant is not preferrable, only as a kind of temporary version until the bank card integration version is established.
Modified banking chip. Another variant is that the core banking chip is modified so that it controls the display, buttons, etc. This procedure seems to be very complicated and may need years to pass the necessary technical and administrative stages. It is definitely not recommended.
Buttons on the Card
The Display-TAN bank card has two buttons: On/OK and Off/Cancel. The Off/Cancel button could possibly be dropped because the card automatically turns off after ca. 20 seconds of inactivity. The cancel button was added mainly for legal reasons: this way the customer can end the confirmation of a malicious money transfer in a defined way. But of course, he could as well stop proceeding.
Display-TAN as a successor of NFC-TAN
Display-TAN's predecessor NFC-TAN has three severe problems:
- NFC-TAN is not as secure as ChipTAN,
- NFC-TAN does not work with iPhones and iPads,
- NFC-TAN needs a change of the core bank chip - what takes a lot of time, technically and regulatory.
- Display-TAN reaches the security level of ChipTAN - because of the display.
- Display-TAN can be used with iPhones - because of Bluetooth instead of NFC.
- Display-TAN is easier tho integrate into existing bank cards - because it comes as a blank plastic card, i.e. the current banking chip does not have to be modified.
Advantage of NFC-TAN: no hardware costs, no running costs.
TAN-generating algorithm
The current Display-TAN demo card produces the TAN via OATH/OCRA, see this page for details. But also EMV/CAP can be implemented, or a custom algorithm.